Blog
June 7, 2024
Software Change Impact Analysis: 3 Benefits of Knowing What Your Code Will Do Before You Merge
Infrastructure Automation,
How to & Use Cases
When’s the last time you did something without knowing how it could turn out? Surprises can add a little excitement to your day-to-day, but one place they’re not really welcome is in infrastructure code. That’s why we have change impact analysis, a method of predicting the effect one change can have on other parts of a system before you make it. Software change impact analysis, as you might imagine, assesses how changes to a piece of software can affect other parts of the same system.
Change impact analysis is all about knowing what could happen before a change is made so you can make the right choice — no matter what that choice is. Let’s dig into the concept, some of its use cases and steps, and an example of conducting a software change impact analysis before tweaking infrastructure code.
Back to topWhat is Impact Analysis in Software Development?
In software development, change impact analysis is the process of defining, evaluating, and measuring how changes in an application can have consequences elsewhere in a system.
Impact analysis is used in the planning and design phase of the software development lifecycle. Software change impact analysis helps you identify what technologies or configurations will be impacted when you make a change somewhere else in the system. For example, conducting an impact analysis before you launch a new microservice can give you a heads up on potential integration issues with the services and dependencies that already exist.
The main benefit of change impact analysis for software is that it helps avoid unexpected consequences. Basically, knowing what could happen as a result of new code deployments can help you prepare for or even sidestep negative impacts, like downtime and rework.
Back to top3 Reasons You Should Be Doing Impact Analysis for Your Infrastructure Code
Look — writing clean code is one of the most important practices in software development. Making sure your infrastructure code is clean, concise, structured, and contextualized (yes, including your Puppet code!) can help you avoid rework, reduce tech debt and error rates, and generally makes everyone’s jobs easier.
But even if you could write perfect, squeaky-clean code, a code impact analysis can give you a heads up on the far-reaching consequences of new code deployments, especially for changes to critical infrastructure code.
That’s because no amount of clean code can insulate your infrastructure against the ripple effect the most innocuous code deployments can have: Complex interdependencies, risk management, compliance, scaling policies, stability, on and on and on. (To all the engineers and devs reading this, that doesn’t let you off the hook! Stick to style, leave helpful comments, and remember: less is more!)
The benefits of doing impact analysis for your infrastructure code changes are…
- Minimizing risk: When you know what could happen, you can choose the path that has the least negative impact.
- Managing costs: If a code change leads to more problems for your team, it could cost more money than it’s worth — service downtime, billable hours, and even compliance fines. With impact analysis, code changes to IT resources are delivered more quickly, more securely, and with bigger business outcomes in mind. Code impact analysis helps speed up innovation, protect revenue, decrease costs, and reduce risk.
- Enhancing agility: Sometimes, the results confirm something you expected. In that case, impact analysis gives you confidence knowing the outcome will align to what you expect. Other times, it detects changes that pose a risk. At that point, you have the option to either accept that risk and push anyway, or make some changes before pushing code. Ultimately, the value of code impact analysis gives is that it gives you the option. Sharing an impact assessment with other stakeholders, like business leadership, can help them decide whether the benefits of the change justify the risk.
Factors to Consider When Conducting Software Change Impact Analysis on Infrastructure Code
Every change to your infrastructure code is different — even unpredictable (hence the whole concept of impact analysis). So if you’re going to systematically evaluate the impact of code changes across your infrastructure, you need to have a clear idea of the components that could be impacted.
Here’s a checklist of components you should consider when analyzing the impact of changes to infrastructure code:
Component | Description | Impact Analysis Can Show You… |
Compute Resources | Servers, VMs, containers, and other instances running applications and services | How the change impacts the instances running your application |
Networking | Load balancers, virtual networks, and firewalls | Effects on load balancers and network traffic |
Storage
| Databases, warehouses, file storage, and block storage | How increased or decreased instance counts affect database connections and performance |
Application Components | Microservices, middleware, and APIs | How your code change will impact API response times |
CI/CD Tools | CI/CD pipelines and IaC tools | What adjustments you need to make in deployment scripts to handle scaling changes |
Monitoring and Logging | Monitoring tools like Datadog and logging tools like Splunk | Whether or not your monitoring can scale with infrastructure to catch performance issues |
Security Components | Security automation tools including identity and access management (IAM) like role-based access control (RBAC), encryption, and more. | Whether or not your security groups and IAM roles are correctly configured for scaled instances |
Integrations | Third-party services and APIs and databases outside the primary environment | How scaling affects third-party services and data flow |
How to Do Change Impact Analysis in Software Testing (Examples & Steps)
So what kinds of changes are we talking about, anyway? While impact analysis is pretty well known in the business world, it might not be obvious to those in IT. To connect the concepts, here’s an example of what we mean when we talk about code impact analysis.
Imagine you’re a sysadmin who needs to change the auto-scaling settings in your cloud infrastructure to dynamically adjust allocations based on traffic. You write the code that adjusts the cloud scaling settings, then you test it in your continuous delivery pipeline to make sure it’s clean before requesting to merge it — but you still can’t be sure what else that code could do when it’s deployed. That’s where code impact analysis comes in.
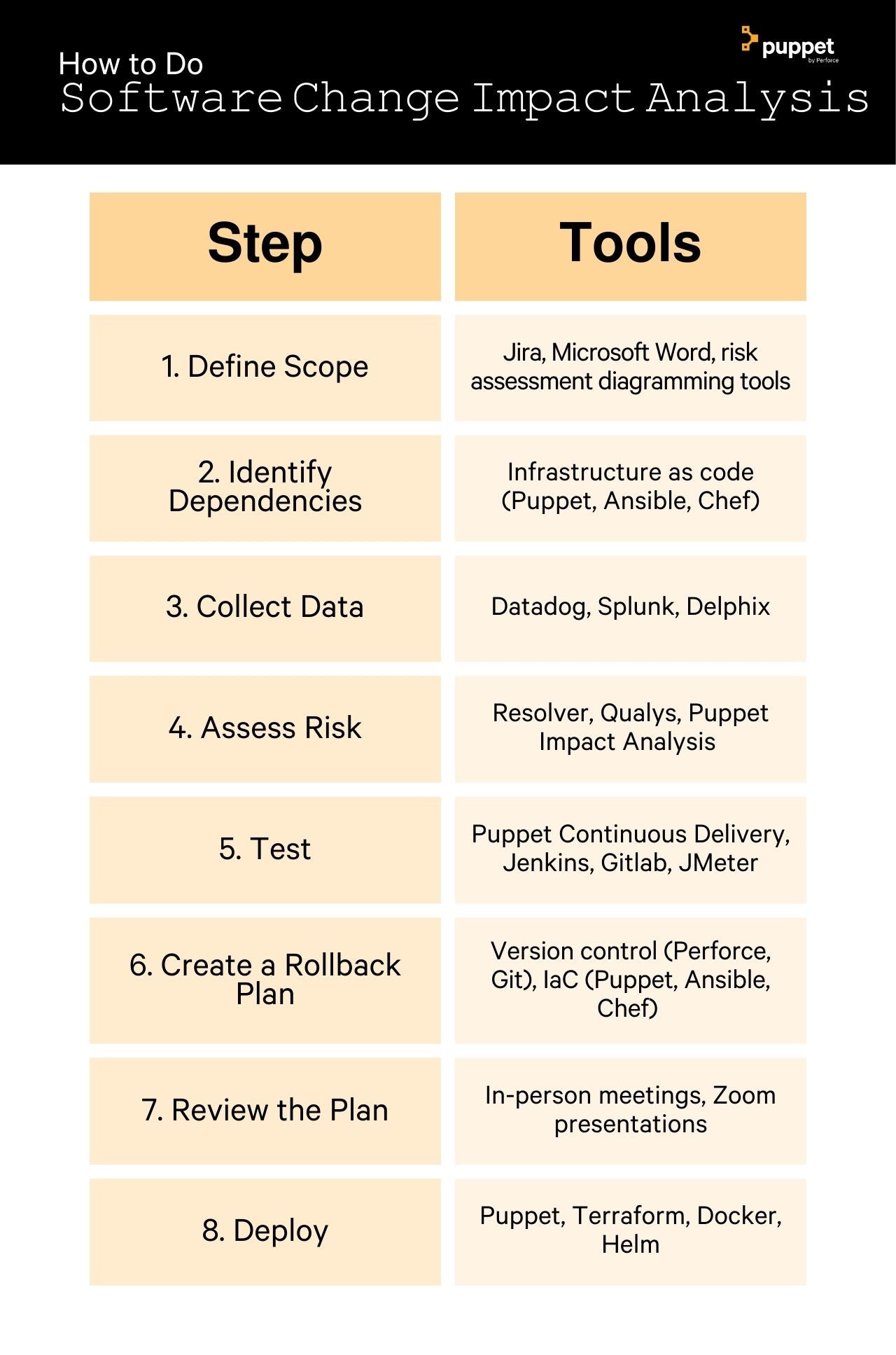
Impact Analysis Step | Description | Tools for Doing It |
1. Defining Scope | Clearly outline the proposed changes to the infrastructure code to assess the situation. What do you want to do to your infrastructure code? What is the intended function or purpose of the change? | Jira, Microsoft Word, risk assessment diagramming tools like Gliffy |
2. Identifying Dependencies | Map out the connections between the servers, VMs, storage, cloud security, services, and other components that could be impacted by your infra code change. | Infrastructure as code (Puppet, Ansible, Chef) is really handy here, because it structures configurations, dependencies, properties, and other facts about your infrastructure in a version-controllable way. |
3. Collecting Data | How does your system typically perform? What metrics should you watch to measure the effect of your proposed change? | Datadog, Splunk, Delphix |
4. Assess Risk | Will your infrastructure code changes cause downtime? Does changing the auto-scaling settings open you up to new security vulnerabilities? On the other hand, what do your stakeholders stand to benefit as a result? | Resolver, Qualys, Puppet Impact Analysis |
5. Design & Conduct Tests | Create plans for unit, integration, and performance tests as part of your CI/CD pipeline. | Puppet Continuous Delivery, Jenkins, Gitlab, JMeter |
6. Create a Rollback Plan | Make sure backups are tested, available, and documented in case you need to revert your changes. | Version control systems (Perforce Helix Core, Git), infrastructure as code (Puppet, Ansible, Chef) |
7. Review the Plan | Use the data from step 3 to gain approval from stakeholders to deploy the change. Present the metrics that make the most sense to your audience (developers, IS ops, business leaders), and be ready to answer their specific questions. | Good old-fashioned in-person meetings and Zoom presentations |
8. Deploy | Roll out the changes carefully (with canary releases or blue/green deployment) and monitor the affected environments to get alerts in case of trouble. |
The Best, Fastest Way to Analyze the Impact of Infrastructure Code Changes
Some of the most complex infrastructure in the world is built and managed with Puppet. Impact Analysis is a premium feature for Puppet Enterprise that shows you the potential impact of new Puppet code on your existing Puppet infrastructure configurations. Adding it to a control or module repository’s CI/CD pipeline automatically generates a report based on every proposed change to that repository.
We created Impact Analysis to help Puppet Enterprise users move faster with less unwanted risk so they can minimize downtime and plan around unexpected consequences they might otherwise have missed.
Start using Puppet Impact Analysis to start committing infrastructure code changes with confidence. Not using Puppet? Learn more about Puppet Enterprise and request a demo at the link below.


