Blog
February 4, 2025
Struggling With Your Patch Management Process? Template, Essential Steps & Tips for a Stress-Free Patch Management Procedure
Infrastructure Automation,
How to & Use Cases
A patch management process lays out the steps associated with updating software and hardware. The typical patch management procedure includes things like prioritizing important patches, testing them, and eventually deploying them on an automated schedule — but with so many tools for managing patching in so many different kinds of setups, no two IT teams’ patch management processes look alike.
What does your patch management process look like? Are you always ahead of the game and ready to patch on time, or are you usually behind schedule and not sure where you’re getting stuck? In this blog, we'll break down the steps of a basic patch management process and offer a few of our top tips to help improve your patch testing and rollout.
Back to top
What is a Patch Management Process?
The steps of a patch management process include monitoring for new patches, testing patches, deploying patches, and documenting the patches applied. A patch management process helps reduce mistakes and prevent bugs and vulnerabilities when patching systems.
A patch management process is crucial for updating servers, software, hardware, firmware, and network devices on time. But there’s no single prescriptive patch management process that works for everybody; in reality, a lot of organizations try a lot of different tools and methods for patch management until they find something that works for them.
Broadly speaking, a patch management process includes:
- Deciding on a schedule for when patches should roll out.
- Setting up a testing process to make sure that patches will work in your environment.
- Creating a plan for managing risk when something goes wrong.
- A plan to let users know what changes have occurred as a result of a patch.
If you’ve got a disciplined approach to patch management, chances are good that it looks like the list above. The “when” and the “how” are between you and your team. Which patches are most important (or even mandatory); which you can skip (and for how long); when you deploy them; what kind of warning you give system users before rebooting their systems — those are all for your IT team to decide.
But before you decide any of those things, and before you pick a patch manager, you should have a few more details nailed down. So here’s a list of important steps in the patch management process to help orient your plan.
Back to topPatch Management Process Template: A Step-By-Step List for Patching Success
Get this list as an easy-to-follow onesheet — | 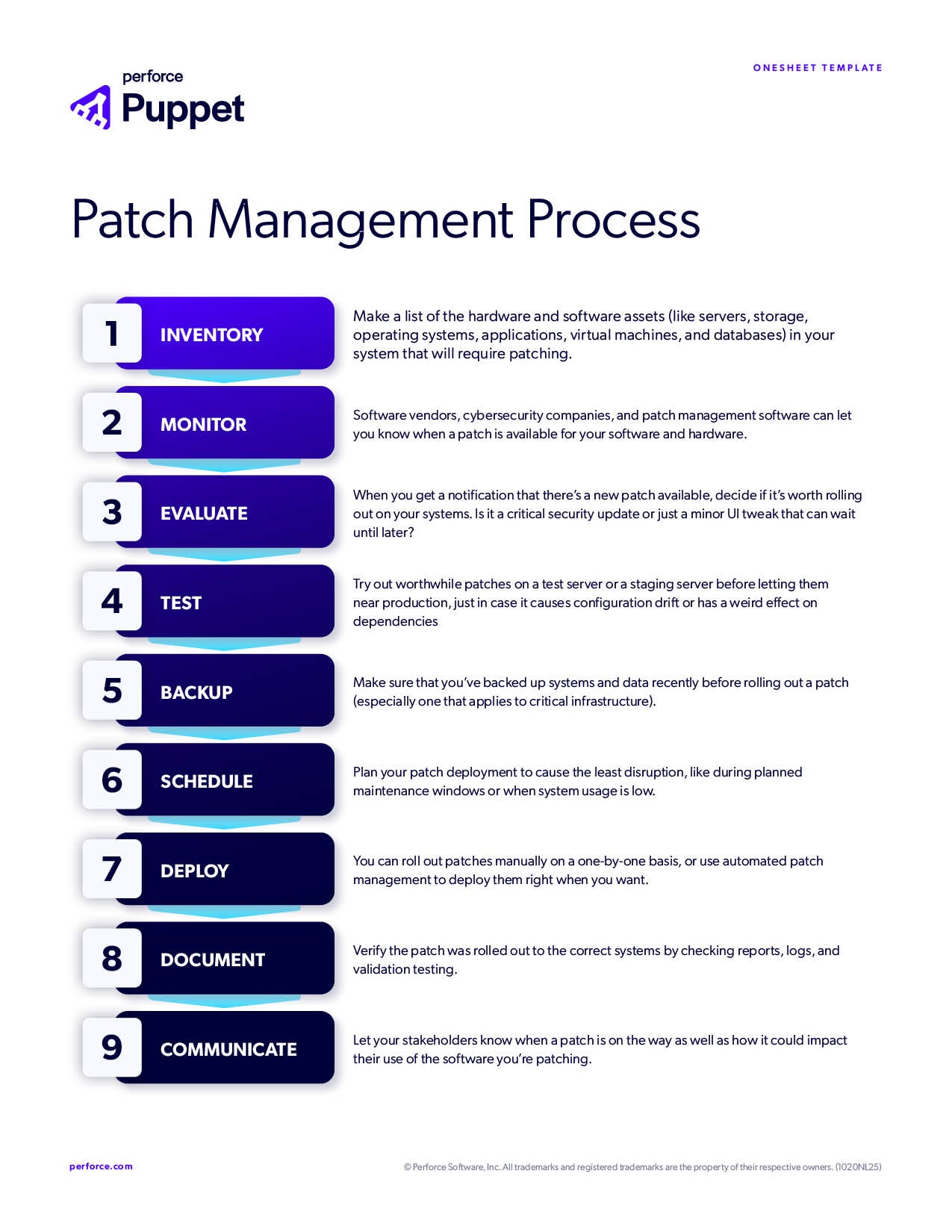 |
Step | Description |
Inventory | Make a list of the hardware and software assets (like servers, storage, operating systems, applications, virtual machines, and databases) in your system that will require patching. |
Monitoring | Software vendors, cybersecurity companies, and patch management software can let you know when a patch is available for your software and hardware. |
Evaluation | When you get a notification that there’s a new patch available, decide if it’s worth rolling out on your systems. Is it a critical security update or just a minor UI tweak that can wait until later? |
Testing | Try out worthwhile patches on a test server or a staging server before letting them near production, just in case it causes configuration drift or has a weird effect on dependencies. |
Backups & Snapshots | Make sure you have current backups and/or snapshots before rolling out a patch. You'll thank yourself later if something didn't get caught in the testing process and brings your server down. Puppet Plans and Tasks are a great way to not only automate backups and snapshots but include it as part of your default patching process. Infrastructure as code is a great way to do this, because it turns your infrastructure-wide configurations into code you can change, repeat, back up, and restore quickly. |
Scheduling | Plan your patch deployment to cause the least disruption, like during planned maintenance windows or when system usage is low. |
Deployment | You can roll out patches manually on a one-by-one basis, or use automated patch management to deploy them right when you want. |
Documentation | Verify the patch was rolled out to the correct systems by checking reports, logs, and validation testing. Infrastructure as code saves a lot of time on this step by automating documentation and reporting as version-controllable code. |
Communication | Let your stakeholders know when a patch is on the way as well as how it could impact their use of the software you’re patching. |
Now, while that list might seem fairly comprehensive, you’d be surprised at how easy it is for patching to get off track. Even once you’ve got a repeatable structure underneath your patching process, you’ll start feeling the friction here and there. A script will fail and a big patch won’t go out on time; a zero-day drops too fast for your testing process to keep up; a cron job fails and suddenly your users’ machines are rebooting midday on a Wednesday instead of in your defined maintenance windows.
The good news about patching is that there’s always room to improve. Here are four tactics we recommend for putting a better patch management process in place, even if you’re already automating every step listed above.
Back to top4 Steps to a More Effective Patch Management Process
Putting off patching is a notoriously common issue in IT, especially in multi-OS systems, where patching can be a huge pain. But building your patch management process with half-measures will lead to missed updates, inconsistent hardening, performance issues, and an increased susceptibility to vulnerabilities and cyberattacks.
Make Sure Your Inventory is Up to Date | Enforce & Review Your Specific Policies |
Don’t wait for new devices and users to surprise you when a patch needs to take place. Make sure you’re keeping an accurate inventory of all the software you have on your network, and when they will need to be patched. But what exactly is the risk if you don’t ensure that your inventory is up to date? You need to know what software you have so you know to watch for updates. If someone is running an app and you don’t know about it or don’t update it, a patch for a critical vulnerability could go unnoticed. | Your patching policy should be established before any patching takes place. It will include the schedule for patching, how you test, how you react to issues that arise, and the way that you communicate updates to your users. Enforcement is key — standardizing the way that you patch will help smooth the process for everyone involved. Regularly reviewing your existing policy is also critical. Patch management is an evolving process and 'exceptions' should be reviewed to ensure the process works for them too. |
Monitor & Report | Demonstrate & Publish |
Perhaps the most critical part of patch management is monitoring for new patches to ensure you’re current with the latest versions of everything you use. As mentioned earlier, infrastructure as code is great for automatically documenting changes from your desired state (especially when used in a policy as code manner), which makes patch reporting an automated breeze. | Customers will always express concern over downtime and failures. Record and publish that data. If the data shows your patching isn’t effective, find out why and fix it. Patching can be difficult, especially if the delta from ‘current version’ to ‘installed version’ is high. That data in itself is valuable as it demonstrates to the customer that the longer you leave it, the higher the risks. |
The Mistakes that Can Destroy a Patch Management Process
Improper testing, poor communication, and custom scripts are great ways to bungle any patch management process.
We’ve been helping organizations big and small smooth out their patch management for a long time. We’ve seen some great patching processes and some… not-so-great ones. Take it from us: When a patch management process breaks down, it’s almost always for one of these three reasons.
Skimping on Testing
Your testing should be more than a “pass/fail”. To get the most out of the patch testing process, you’ve got to involve end users and application owners. Engage them to get their insights about how patches might affect their workflows or app performance, and create feedback loops to let them report issues and find problems early.
Another way to improve your patch testing is by creating a decision matrix that outlines your next steps based on the outcome of a test. It’ll tell you whether you should proceed with deployment, delay for more testing, or rolling back changes.
Speaking of which, developing failover processes is key to your patch testing strategy. Failover processes can help keep operations running in the event a patch goes wrong. For example, automation tools can roll back changes to a previous system state prior to the failed patch.
Just Blasting Out Patches Without Warning
What communication channels are you using to tell users how patches might affect their experience? Is it a weekly email nobody reads, or a Slack channel that provides regular updates? Talk to your relevant stakeholders about what works best for them to predict and plan their work around your patching strategy.
Also, don’t use system references when communicating with your customers. You may know the owner of the server, but the customer may have no idea what "ddt87app3303pd server" actually is. Instead, help them identify which machine you need to patch — something concrete like “the on-prem database server running Ubuntu 20.04.”
Automating Patching with Just Scripts
Most organizations have some kind of automation set up for finding, testing, and deploying patches. Maybe you use WSUS or very basic configuration management tools along with Bash and PowerShell scripts to download and apply patches. Those might be enough to simply get by for a while, but they’ll eventually become a barrier to a better patch management process.
Back to topUsing Puppet for Patch Management
When you mature your automation tools and strategies to include capabilities like policy as code and continuous compliance, you amplify the benefits of automated patching — like reduced error and less wasted time — and unlock a whole lot of additional value from your vulnerability remediation strategies.
The Puppet Enterprise platform increases efficiency while enhancing infrastructure security with vulnerability remediation features including patch scheduling, blackout and maintenance windows, dynamic node grouping, RBAC, and powerful integrations with existing security scanners. Controlling patching and vulnerability remediation with dedicated features in the Puppet Enterprise console gives more of your team a central control plane from which to mitigate, remediate, patch, and continuously improve.
Here are some key features of using Puppet for patching and vulnerability management:
- CI/CD integration: Integrating patches into your automated CI/CD pipeline lets you continuously test and integrate those software and hardware updates.
- Easy roll-forward and recovery: Testing can help reduce error, but it’s almost impossible to completely eliminate risk when patching. Thus, you apply hotfixes, zero-days, and emergency patches that fix issues introduced in previous patches, rather than reverting the old one. Taking your automation strategy further to include configuration management helps you restore systems and services faster in case of critical error.
- Policy enforcement: Writing your desired infrastructure state as repeatable code makes it easier to make sure your patching processes don’t throw your systems out of alignment with internal and external compliance policies.
- Patching across operating systems: If you’re trying to patch Windows and Linux servers in the same fleet, for example, scripts and SCCM and WSUS won’t cut it. Agent-based automation is OS-agnostic, so you can monitor, test, deploy, and validate patching across multiple OSes at the same time.
Puppet is agent-based automation and configuration management that enables desired state management and policy as code approaches to patching. Using Puppet for patching gives you flexibility to patch your way knowing that the state of your system is secure and continuously enforced, even across hundreds of thousands of servers.
- Puppet can apply patches with manual triggers, scheduling, and via API.
- The Puppet agent runs every 30 minutes by default (that’s 48 times every day) to continuously enforce your desired system state. That means once you’ve set your configurations as code, your systems are never out of policy for long.
- Puppet agent-based automation doesn’t rely on SSH to deploy code on managed nodes, so you can apply scheduled patches even during network outages.
- The Puppet agent can be installed on Windows and Linux OSes, so you can roll out (and roll back) patches across complex IT environments simultaneously.
Puppet for Patching Customer Story: Salesforce
Salesforce used to host a “Patching Party'' where several members of their IT team spent hours testing and manually applying patches. Now that they’re using Puppet, they can push a single line of code and apply a patch to all servers at once. Read the Salesforce Puppet case study here.
Puppet Enterprise Advanced Makes Patching Easier.
The most powerful version of Puppet adds time-saving features for patch management, like a GUI, dynamic node grouping, RBAC, previews of IaC deployments, self-service, and integrations that make it even easier to visualize and orchestrate patching across all of your systems.
Get a look at Puppet Enterprise Advanced in action by filling out the form on our Demo Request page, or learn more about using Puppet for patch management on our automated patch management use case page.

