Blog
June 6, 2024
CIS Benchmarks Explained: Levels & Steps for Quick CIS Benchmark Compliance
Security & Compliance,
How to & Use Cases
CIS Benchmarks are important for security and compliance. In this blog, you'll get an overview, plus learn how to enforce CIS Benchmarks with Puppet.
Back to topWhat are CIS Benchmarks?
CIS Benchmarks are essentially checklists of best practices for IT security. They outline security configurations for operating systems, databases, applications, and more. CIS Benchmarks are created by experts at the Center for Internet Security (CIS), which offers them as free downloads.
There are more than 140 CIS Benchmarks to date, and they’re all created by industry consensus. That means that instead of being handed down by a small group, each benchmark is created by a community of cybersecurity experts, compliance and security practitioners, and organizations dedicated to improving global cybersecurity.
👉 Start Automating CIS Benchmarks Today with a Free Trial of Puppet 👈
Each CIS Benchmark can be applied to multiple technologies and they aren’t specific to any one vendor or platform.
While many compliance frameworks are broad, CIS Benchmark recommendations are known for providing specific action steps and changes to implement to improve security at the system and app levels.
On this episode of the Puppet podcast, we talk to the Chief Information Security Officer at the Center for Internet Security about how CIS Benchmarks help organizations keep up with the rise of threats and vulnerabilities in the modern cybersecurity landscape.
CIS Benchmarks are flexible and can be implemented at different levels (Level 1 and Level 2), which allows different organizations to define the level of security that’s right for them. CIS regularly updates CIS Benchmarks so they address the changing cybersecurity threat landscape.
Back to topCIS Benchmark Categories
CIS Benchmarks are categorized by the area of IT they help secure. The seven main categories of CIS Benchmark are:
- CIS Benchmarks for Operating Systems (OS) cover securing configurations for Windows, Linux, and macOS.
- CIS Benchmarks for Servers include security configurations for server software like WIndows Server, SQL, VMWare, Kubernetes configuration, and more.
- CIS Benchmarks for Cloud Providers secure cloud infrastructure from AWS, Azure, and GCP.
- CIS Benchmarks for Network Devices provide security configuration guidelines for network devices, including hardware vendor-specific guidelines for CISCO, Palo Alto Networks, and Juniper.
- CIS Benchmarks for Desktop Software cover configurations to ensure security for common desktop applications like Microsoft Office, Microsoft Exchange Server, Chrome, Safari, and Firefox.
- CIS Benchmarks for Mobile Devices like iOS and Android address OS privacy configurations, settings, permissions, and dev options on mobile devices.
- CIS Benchmarks for Multi-Function Print Devices include configuration recommendations for multi-function printers in an office setting. Recommendations from CIS include firmware updates, TCP/IP config, file sharing, wireless access, and user management.
CIS Level 1 Benchmarks Explained
Level 1 CIS Benchmarks include basic security requirements that can be used on any system and have a smaller impact on service and functionality.
Who Should Use Level 1 CIS Benchmarks?
Organizations who only need to achieve a basic level of cybersecurity often find value in implementing Level 1 CIS Benchmarks. Those often include:
- Small and medium-sized businesses with limited cybersecurity resources and few compliance requirements
- Organizations without critical systems like personally identifiable information (PII) or other sensitive data storage or processing
CIS Level 2 Benchmarks Explained
Level 2 CIS Benchmarks are stronger than Level 1, but they can actually hinder functionality if they’re not implemented correctly.
Who Should Use Level 2 CIS Benchmarks?
Level 2 CIS Benchmarks are more comprehensive than Level 1, and implementing them often requires more testing and operational changes. Organizations that handle more sensitive data or are at a greater risk for cybersecurity threats often opt to implement Level 2 CIS Benchmarks. That can include:
- Enterprise organizations with vast, complex IT environments that span data centers and multi-cloud deployment or hybrid cloud IT
- Organizations that host critical infrastructure for services like energy, communications, healthcare, and transportation
- Regulated industries like healthcare and financial services organizations
- Organizations with high cybersecurity risk like government and banking
CIS Level 1 vs Level 2: What's the Difference?
Broadly speaking, CIS Benchmarks Level 1 are easier to implement and more broadly applicable than Level 2, but they're not as stringent. Level 2 benchmarks are more thorough and provide a higher level of security, but they might take more time and effort to implement on your own.
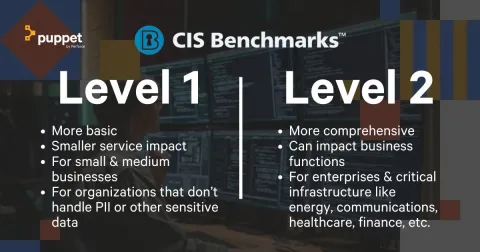
One of the benefits of using CIS Benchmarks is that you can select which level of CIS Benchmark compliance applies to your organization. Sometimes, regulatory frameworks and industry standards may specifically require CIS Level 1 or CIS Level 2 compliance.
Some small organizations may be subject to a high degree of regulatory oversight and may opt for Level 2 CIS Benchmark compliance. Certain large organizations may find that Level 1 CIS Benchmark compliance is satisfactory for their cybersecurity need.
Each organization’s compliance needs are different, and there are no hard-and-fast lines defining which organizations need which kind of compliance in every situation.
Back to topWhy Should You Use CIS Benchmarks?
CIS Benchmarks provide instructions for securing systems, apps, networks, and infrastructure. They're free, globally recognized, and can be customized to the needs of almost any organization.
CIS Benchmarks are Created by Experts
CIS uses a consensus-driven approach to develop its benchmarks. This two-step process starts with cybersecurity and system experts, who define, review, and test the recommendations. Those experts come from a range of backgrounds including government, research institutions, and the private sector.
Once they reach consensus, they solicit feedback from a wider range of cybersecurity professionals from around the world.
This process is a stress test for each benchmark. It makes sure that the benchmark is defined, refined, and actionable for enforcing security and compliance.
CIS Benchmarks are Free
Really! You can go to the CIS Benchmark page for any OS, app, or other covered technology you want, fill out a simple form, and download the relevant CIS Benchmark files.
CIS Benchmarks are free to use under the Creative Commons License. That means you can implement, share, and adapt them to fit your documentation and processes for non-commercial purposes with attribution/credit to CIS.
They Help You Comply with Regulations
Both CIS Level 1 benchmarks and CIS Level 2 benchmarks align with many of the major regulations that are required for various industries.
With so many different regulations to keep up with, it’s no wonder that companies fall behind in compliance. CIS has aligned its benchmarks against many regulatory frameworks, enabling companies to utilize the benchmarks to gain best practices from CIS that help them achieve CIS compliance against the regulations that apply to them.
They're Globally Recognized
Because CIS Benchmarks are created by a body of international experts, they're accepted by organizations around the world.
While we're not aware of any regulatory bodies that explicitly require CIS compliance as their only standard, CIS Benchmarks can be used to achieve FedRAMP accreditation, SOX compliance, NIS2 compliance, and more.
Back to topCIS Benchmark Tool: Puppet
Puppet Enterprise has the CIS-CAT® Pro Assessor built in, which tests infrastructure configurations against CIS Benchmarks. The Security Compliance Enforcement premium feature automatically remediates security baselines to configurations hardened against CIS Benchmarks.
Pairing CIS Benchmarks with Puppet’s powerful automation capabilities goes a long way towards a more compliant and secure infrastructure. Here's how Puppet automation and configuration management are used as a CIS Benchmark tool.
Puppet Enterprise for CIS Benchmark Assessment
Puppet Enterprise features an integrated version of the CIS-CAT® Pro Assessor. It lets users check their infrastructure configurations for alignment with CIS Benchmarks from right within the Puppet Security Compliance Management console.
But Puppet's agent-based automation model is where it really shines for CIS compliance. The Puppet agent on each target server operates autonomously, managing and executing tasks independently without needing constant human oversight. That means the CIS-CAT® Pro Assessor in Puppet Enterprise assesses configurations directly on the actual OS where it's installed.
Security Compliance Enforcement: Automatic Remediation to Hardened Security with CIS Benchmarks
Security Compliance Enforcement is a premium feature available for Puppet Enterprise and Open Source Puppet that automatically remediates drifted configurations to bring them back into compliance with the relevant CIS Benchmarks.
Security Compliance Enforcement saves you the time of manually coding compliant configurations for each OS in your Puppet infrastructure. It uses Puppet's same agent-based automation runs to enforce hardened security baselines across heterogeneous Windows and several Linux distributions on-prem, in the cloud, and in hybrid setups.
Not Using Puppet to Manage Secure, Compliant Infrastructure?
With 10 nodes free, you can get a taste of managing servers with the CIS features built into Puppet Enterprise. Start your free trial of Puppet Enterprise today.
